Profiler
The Profiler sample demonstrates the functionality of the nRF Profiler subsystem. It shows how to use the Profiler to log and visualize data about custom events that are not part of the Application Event Manager.
Requirements
The sample supports the following development kits:
Hardware platforms |
PCA |
Board name |
Build target |
|---|---|---|---|
PCA10090 |
|
||
PCA10095 |
|
||
PCA10040 |
|
||
PCA10056 |
|
||
PCA10112 |
|
When built for an _ns build target, the sample is configured to compile and run as a non-secure application with Cortex-M Security Extensions enabled.
Therefore, it automatically includes Trusted Firmware-M that prepares the required peripherals and secure services to be available for the application.
Overview
The sample initializes the nRF Profiler and registers and periodically profiles the occurrences of the following event types:
Event without data (
no data event) - This event is used to signal the occurrence of an event only. It does not contain additional data.Event with data (
data event) - There are several numerical values associated with this event. The values are updated periodically.
Configuration
See Configuring and building an application for information about how to permanently or temporarily change the configuration.
Building and running
This sample can be found under samples/nrf_profiler in the nRF Connect SDK folder structure.
When built as firmware image for the _ns build target, the sample has Cortex-M Security Extensions (CMSE) enabled and separates the firmware between Non-Secure Processing Environment (NSPE) and Secure Processing Environment (SPE).
Because of this, it automatically includes the Trusted Firmware-M (TF-M).
To read more about CMSE, see Processing environments.
To build the sample with Visual Studio Code, follow the steps listed on the How to build an application page in the nRF Connect for VS Code extension documentation. See Configuring and building an application for other building scenarios, Programming an application for programming steps, and Testing and optimization for general information about testing and debugging in the nRF Connect SDK.
Testing
After programming the sample to your development kit, you can test it by performing the following steps:
Go to the
scripts/nrf_profilerfolder.Run the script
real_time_plot.py, with the name that should be used to store the data as the argument. For example:real_time_plot.py test_name
This command generates a
test_name.csvfile and atest_name.jsonfile. The script opens a GUI window that displays events as dots on timelines, similar to the following diagram.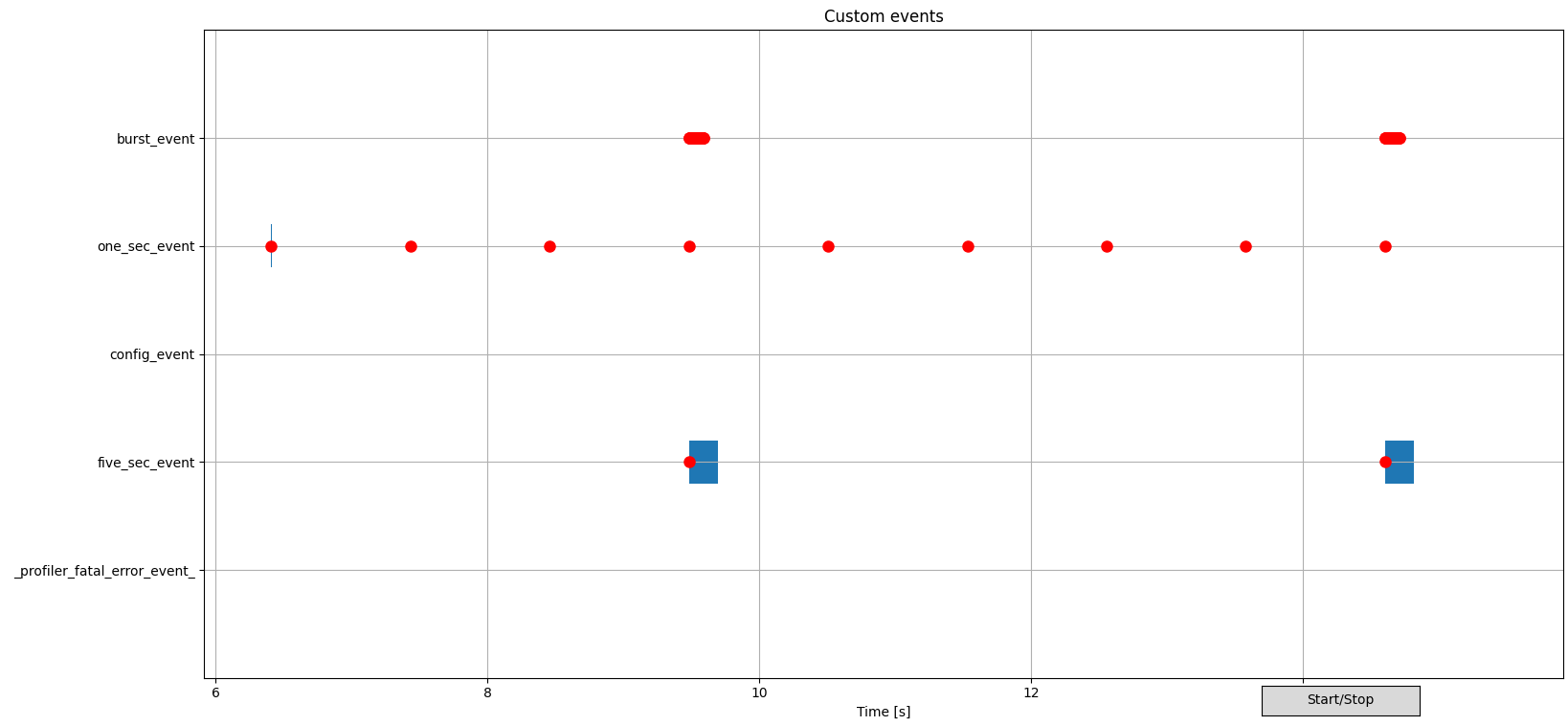
Example of nRF Profiler backend script visualization
See the Backend visualization section in the Profiler documentation for more information about the GUI.
Connect to the kit with a terminal emulator (for example, nRF Connect Serial Terminal). See Testing and optimization for the required settings and steps.
After you connect, the sample will display messages in the terminal.
Dependencies
This sample uses the following nRF Connect SDK subsystems:
In addition, it uses the following secure firmware component: